Bitwarden Chrome extension is a password manager solution in the open-source category. Apart from the Chrome OS or browser, the user can also use extensions available for Mozilla Firefox, Microsoft Edge, Opera, Safari, Vivaldi,
Brave and Tor Browser.
Using the AES-256 encryption the Bitwarden is one of the best open-source password managers that comes with an ability to not only store password in almost all major platforms but also allows to sync them across all devices free of cost.
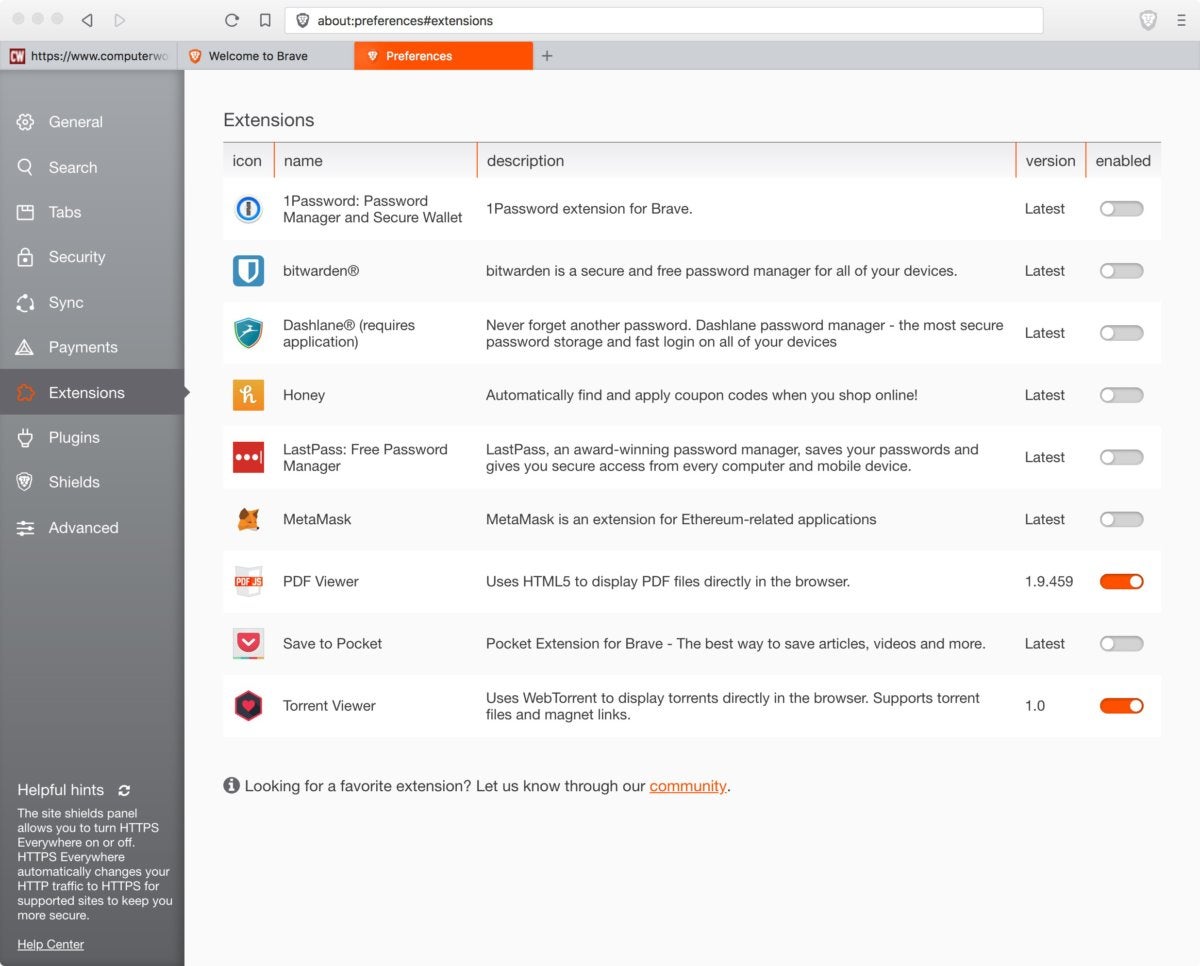
Importing from other password managers such as 1Password, LastPass or Chrome is possible, but not via the Windows, macOS, Linux clients, or extensions, but only via the web interface. Therefore, the user has to log into the web vault at https://vault.bitwarden.com and then navigate to Tools → Import Data.
Apart from the regular login information and password, the software can also store secure notes, credit cards, and important identity information.
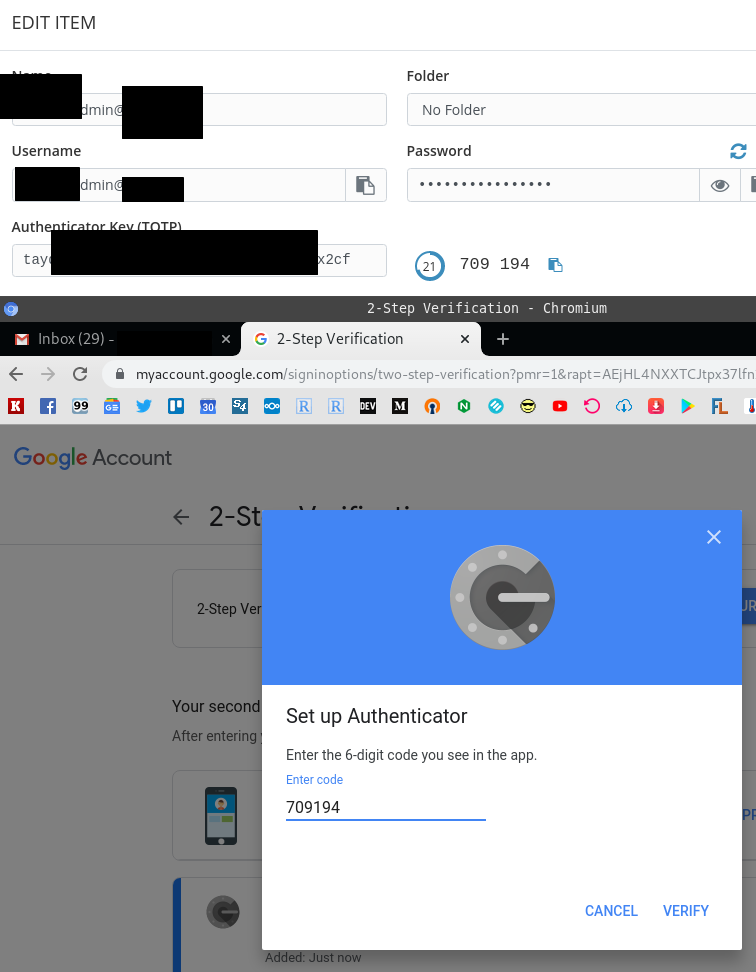
To enhance security further the free version also offers two-factor authentication, however, as compared to other best password manager options such as Dashlane, LastPass, Zoho Vault some features are missing such as security check on passwords. Here is the complete listof other password manager services from where the user can Import their all password to Bitwarden.
Bitwarden is a highly sensitive security application managing 100 and more passwords. It is not a good idea to have this application require additional permissions to communicate with other applications. I rather take this as a worrying indication that the development of Bitwarden is turning into a bad and sad and wrong direction. Bitwarden makes it easy for you to create, store, and access your passwords. Bitwarden stores all of your logins in an encrypted vault that syncs across all of your devices. Since it's fully encrypted before it ever leaves your device, only you have access to your data. Not even the team at Bitwarden can read your data, even if we wanted to.
Well, here we are only to discuss the way to get the Bitwarden Chrome extension and how to use the same to save various passwords. Thus, let’s focus on that. The following tutorial will be the same for Windows, Linux, macOS, and other Desktop operating systems using the Chrome or Chromium browser. Also see: Best free Password managers
Step 1: Open Chrome browser and click on this link- browser extension, it will take you to the extension page of this product.
Step 2: Now, to install the Bitwarden chrome extension, just click on the “Add to Chrome” button. After that a pop-up will appear, click the “Add extension“.
Step 3: You will see a Shield icon in the Chrome Address bar. Click that to see further options of Bitwarden.
Step 4: If you already have an account with this open-source password manager service then use that by clicking on the Login option otherwise use the “Create Account“.
Step 5: A new account will require an email address and also ask you to create a password for your new account which will also be used as a Master password to access passwords, credit cards, Identity, and Secure Notes on other devices as well.
Step 6: Under the Vault, we can create a new Login entry to save some passwords and other items.
Digimon data squad episode 1 in hindi. Password Generator is also there to create strong passwords and use them with various services.

Under the settings tab, the user can change security settings; auto logo out for the vault; can set up two-step authentication, and more…
During our usage Bitwarden chrome extension did a good job to autofill the saved login information for various social accounts and other websites, however, due to security reasons, the auto fill of login forms is not applicable for bank details, and for that, the user has to copy and paste them manually.
Będzie po angielsku bo może przyda się światu. ;)
Short instruction how to run Bitwarden service on home Qnap NAS.
Install „Container Station” on your Qnap. On the left panel of” Container Station” click on „Create” button and then on „Create Application” in upper right corner of window. In the text input field put content of the following listing and name this new application „bitwarden”.
Accept it and run. What you have really done is Docker Compose YAML configuration file which pulls 3 images from Docker Hub server:
- bitwarden_rs – an unofficial Bitwarden server implemented in Rust language,
- nginx – web server required here as proxy for HTTPS requests,
- bw_backup – a docker image running cron job to backup bitwarden database.
and runs containers of them inside „Container Station”.
You should pay particular attention to the ports configuration, line with „580:80” and „5443:443” frases. „580” and „5443” are outside ports which are open on the Qnap itself. You can change to whatever fits for you but don’t use 80, 443 or 8080 because they are already taken by Qnap own services.
Before you run freshly created application (that’s Qnap Container Station’s name for docker-compose GUI) SSH log into Qnap and go to application folder:
Now, you must create configuration for nginx:
Save it as nginx.conf to /share/Container/container-station-data/application/bitwarden/data/nginx folder.
Now, you have to create self signed certificate to encrypt HTTP requests with SSL. To do this log in to Qnap with SSH and run following commands:
In this repo you’ll find two interesting files: data/ssl/bitwarden.ext:
and script called create_ssl.sh:
You can edit data/ssl/bitwarden.ext to make cert generating easier. Look at this lines:
and this:
Warning: your certificate will be valid only for above domains. I use Pi-hole local DNS to redirect bitwarden.fubar to my QNap IP address.
OK, run create_ssl.sh script and follow instructions. At the and you will find whole new structure of folders with files in ssl 82915g gv 910gl windows 7. directory.
Copy certs and private folders to /share/Container/container-station-data/application/bitwarden/data/ssl.
Now, start Bitwarden application:
Open web browser and go to the URL like: https://bitwarden.fubar:5443, remeber to change domain to same value as in DNS.1 for ssl.
You should see Bitwarden login page:
Time to install and use Bitwarden clients on desktops (macOS, Linux, Windows) and mobiles (Android, iOS) but before you’ll do it first go back to SSH session on you Qnap and copy „myCA.crt” file on your computer.
This file is, root CA certificate that will make your Bitwarden clients think that certificate used to connect is valid even it is self signed by you.
Nfs com free download. Install CA certificate on every host you use with Bitwarden client:
macOS – double click on CRT file and it will open in Keychain Access, add it to System keychain and choose „Always Trust” option,
Linux (Debian/Ubuntu)- https://askubuntu.com/questions/73287/how-do-i-install-a-root-certificate
If your CA is in PEM format convert .pem file to a .crt file:
- Create a directory for extra CA certificates in
/usr/share/ca-certificates:
2. Copy server_rootCA.crt file to this directory:
3. Let Debian/Ubuntu add the .crt file’s path relative to /usr/share/ca-certificates to /etc/ca-certificates.conf:
3a. To do this non-interactively, run:
Windows – don’t use it.
Firefox – go to Preferences -> Privacy & Security -> View Certificates. Click Import, then choose PEM/CRT file, select „Trust this CA to identify websites.”
Chrome – in macOS it uses Keychain so you don’t need to add it again. For Linux check this website: https://thomas-leister.de/en/how-to-import-ca-root-certificate/. Quick hint: go to Settings -> Privacy & Security -> Security -> Manage Certificates and Import.
Warning! Original Bitwarden Desktop client use chromium sandbox so you HAVE TO install CA certificate into Chromium!!!
Bitwarden Edge Chromium Extension
When CA certificate is in right place the last thing is:
before you connect every Bitwarden client must „know” the right address of Bitwarden server.
Run client and click gear icon:
then put your server address in 4 fields:
- Server URL
- Web vault server URL
- API server URL
- Identity server URL
Remember to put it in the following form: https://my.ip.address:myport, in case your server has IP 10.0.0.1 and port 5443 it should be: https://10.0.0.1:5443 like in image below. If you use domain name (as me) you should replace IP with domain:
Now, there’s time to create account, you can do it pointing browser to the very same URL as used above: https://10.0.0.1:5443.
It’s all now ready to use.
Few steps to consider:

Bitwarden Chromium Edge
- store database backup somewhere outside Qnap,
- import data from another password manager,
- set up VPN connection to Qnap to synchronize database when you outside.
UPDATE:
How to update docker images?
- ALWAYS MAKE BACKUP OF YOUR VAULT!!! Export it in JSON from Bitwarden client.
- go to your QNap, run FileStation and zip full content of you application data folder:
Bitwarden Edge Chromium Autofill
- stop application in ContainerStation, remove it. Go to Images tab and pull new version of images: bitwardenrs/server, bruceforce/bw_backup and nginx:1.15-alpine.
- create application as written at the beginnign of this article, don’t run it
- unzip content of previously backup data folder (configuration for nginx, ssl, vault and vault’s backup).
- run application.
Related posts:
